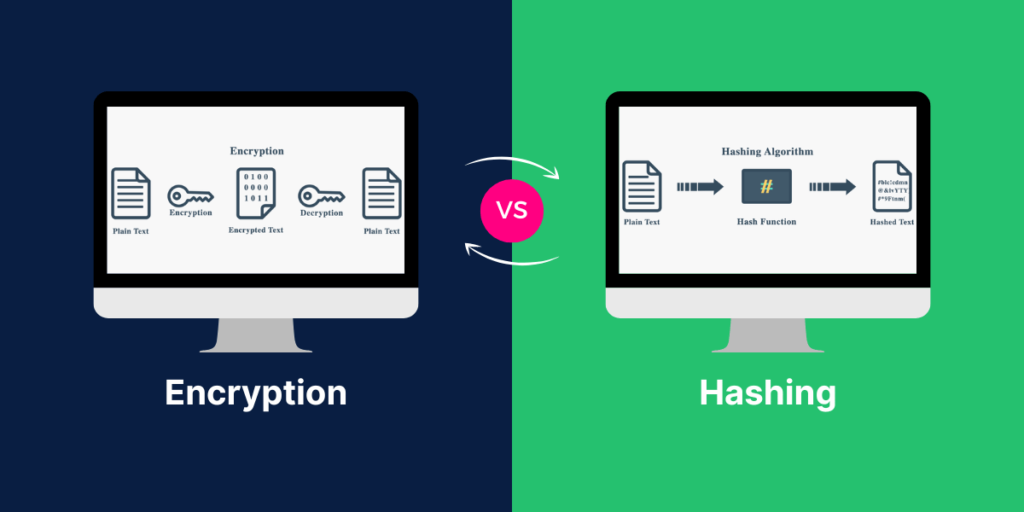
The key differences between encryption and hashing—how encryption secures data for decryption, while hashing provides a one-way method of data protection.
In recent years, the number of intruders has risen sharply. Cybercriminals use the latest technologies to take advantage of weak networks and wreak havoc with the data lying in the servers. In most cases, businesses are lax in ensuring proper systems to thwart such data breaches. It makes them the sitting ducks for hackers who are always looking for vulnerabilities in business networks. Hashing can be used to protect data.
There is a hacking incident every 39 seconds, and it costs businesses around US$ 3.86 million for every data breach. There are various ways to prevent a cyberattack. Companies can use different technologies to prevent a data breach. One of them is through encryption of messages being transferred. But what are they, and what is their use? We will discuss difference between hashing and encryption in more detail in this article.
What is hashing?
The hashing process involves mapping keys and values into the hash table using a hash function. The hash code is usually used to create an index where the value is stored.
Hashing involves a one-way process where an algorithm takes the data and transforms it into a fixed length. It is a hash value, and the length that has been generated is usually smaller than the original string, though it can vary. Here is a details guide on how hashing algorithm works.
What is Hashing
(Source: http://xeushack.com/on-hashes)
Hashing is used to store passwords securely, and no one can access the data. You can avoid duplication, and the algorithm can be used in digital certificates. You can also use hashing to find any specific data from the database.
Salting is a process that is used with the hashing of passwords. A unique value gets added to the password. It gives rise to a different hash value. Salting is used to store passwords. This concept prevents brute force attacks and adds a security layer to the hashing process. Always ensure that the salt for each password is different.
| Hash | Number of bits | Passes | Cracked? | Author | Date launched |
| SHA-1 | 160 | 80 | Yes | NSA | 1995 |
| SHA-2 | None | NSA | 2000 | ||
| SHA-256 | 256 | 64 | None | NSA | 2000 |
| SHA-384 | 384 | 80 | None | NSA | 2000 |
| SHA-512 | 512 | 80 | None | NSA | 2000 |
| MD2 | 128 | 1 | Yes | Ronald Rivest | 1989 |
| MD5 | 128 | 1 | Yes | Ronald Rivest | 1991 |
| HAVAL | 128 | No | Yuliang Zheng, Josef Pieprzyk, Jennifer Seberry. | 1992 | |
| RIPEMD-320 | 320 | No | Hans Dobbertin, Antoon Bosselaers, Bard Preneel. | 1996 | |
| Gost | 64 | No | Soviet union | 1970’s | |
| Whirlpool | 512 | No | Paulo Barreto, Vincent Rijmen | 2001 |
Few hashing technologies
MD5
In the MD5 hash algorithm, you take the string and encode it into a 128-bit output. The MD5 hashes are usually used with a small string. It can also be used to hash data in databases. The algorithm checks whether two sets of data are identical by having a checksum of both sets and then comparing the checksums. However, it is not used now due to vulnerabilities associated with it.
SHA
The Secure Hashing Algorithm (SHA) is a family of six hashing functions. They can take a string of variable length as input and turn them into a fixed-length output. For example, the SHA 0, SHA 1, SHA 224 and SHA 256 operate on a 512-bit message that is divided into blocks of 32 bits each. The SHA 384 and SHA 512 work on 1024-bit blocks divided into 64 bits each.
What is encryption?
Encryption is when a communication message is converted into a secret text that hides the meaning of the information. This encrypted piece of information is called the ciphertext. The process allows the information exchanged with the webserver to be protected from being subject to a data breach. The asymmetric encryption methodology is known as the public-key encryption that is commonly used.
Encryption involves scrambling of the message that can be read only by the authorized set of entities. The process involves converting plain text into random data. The method uses cryptographic keys, a set of values agreed by the sender and the receiver. The data is encrypted before transmitting and is decrypted by the intended recipient.
Two types of Encryptions:
Symmetric Encryption – There is only one key, and the same keys are used for encryption and decryption.
Asymmetric Encryption – It involves the use of a private key and a public key. The private key must not be shared and is kept a secret. The public is known to the user who visits the web server.
The key elements of encryption are:
It is confidential. Unauthorized entities cannot read the encrypted text.
It is authentic. The origin of the message can be traced, thereby ensuring it is genuine.
Encryption also helps by tracking the source of the data that gets leaked in some way. As the origin can be traced, it helps in the authentication of the messages. The messages can be read only by using the requisite keys by the intended entities.
Historical Encryption Algorithms
Before the arrival of modern algorithms, there was an old type of algorithms used. Below are few examples of them:
Shift Cipher: Shift Cipher replaces the alphabets with another positions. For example,
plaintext: A B C D E F G H I J K L M N O P Q R S T U V W X Y Z
ciphertext: X Y Z A B C D E F G H I J K L M N O P Q R S T U V W
if we shift the letter “A’ with “X” and do the same for other alphabets, then an encrypted and decrypted message will look like as below:
Alice: How are you?
Alice Encrypted Text: ELT XOB VLR?
Bob Responded Text: F XJ CFKB
Now, we decrypt above reply:
Bob: I am fine.
In this type of cipher, two parties agree to decide alphabets or numbers for encrypting and decrypt the message. They shift the numbers of alphabets/numbers and creates a decryption/private key.
Substitution Cipher
A substitution cipher is a method of encryption in which units of plaintext are replaced with ciphertext using a fixed system. These units can be a single letter, pair of letters, or mixture of single and pair of letters. The receiver decrypts the message with reverse substitution.
Ransposition Cipher:
Transposition Cipher refers to a regular system in which units of plaintext are moved in such a way that creates a substitution of the plaintext. Rail Fence and Route ciphers are examples of the transposition cipher method.
n the above example, the sentence “WE ARE DISCOVERED FLEE AT ONCE” is written in a grid with proper dimensions. To make it ciphertext, the key has a specified pattern that starts clockwise from the top of the right and looks like as below.
Polyalphabetic Cipher
Polyalphabetic cipher substitution-based cipher that uses multiple replacements of alphabets. Vigenère cipher is an ideal example of the polyalphabetic cipher. There can be many relations or matches between a single plain text character and ciphertext. In this cipher method, plain text letters of various positions are ciphered with different ciphertext alphabets.
Nomenclator Cipher: Nomenclator means a list of words/names. Nomenclator uses a combination of codes and ciphers. This cipher system was popular earlier in the 1400-1850 years. It replaces text with symbols to produce specific decipher codes.

In AES, a plaintext is converted into blocks, and encryption is applied with the encryption key. It includes processes like sub bytes, shift rows, round keys. AES is rapid than the DES algorithm because AES has multiple key length options that make it hard to crack.
PGP –PGP is another extensively spread encryption algorithm which is relatively well-liked as a public key encryption algorithm.
DES: DES (Data Encryption Standard) is a type of Symmetric encryption method which was developed by IBM in 1976 and was adopted by Federal agencies in 1977 for the protection of sensitive and unclassified government data. DES algorithm was included in TLS 1.0 and 1.1 that uses a 56-bit key. This type of algorithm divides 64-bit into two individual 32-bit blocks and the encryption process is applied separately on each block.
The encryption process in the DES method involves permutation, substitution, XOR logical operation, expansion practices.
3DES: 3DES is also known as the Triple data encryption algorithm, which is an upgraded version of the DES algorithm. 3DES came into practice in 1990. It became a part of TLS, SSH, IPsec, OpenVPN. The algorithm applied encryption thrice times on each block that makes it harder to break in comparison to the DES algorithm.
Few Other Encryption Algorithms :
AES: AES (Advanced Encryption Standard) was developed as an alternative to the DES algorithm. The NIST has approved the AES algorithm in 2001. It has different key sizes and block sizes. It has two base functions like substitution and permutation.
Few encryptions technologies
AES (or Advanced Encryption Standard) –
It is usually used in wireless security, file encryption, cheap SSL certificates, etc. It replaced the earlier DES technology as the encryption keys can go up to 256 bits. Several entities use this encryption standard to protect sensitive information. It is considered safe, and it would take a long time to decipher and crack this mechanism.
RSA (or Rivest-Shamir-Adleman named after its creators) –
This involves the factorization of larger integers. The public key has two numbers, and one of them is the product of multiplication between two large prime numbers. The private key is taken from the same two prime numbers. The RSA keys are usually 1024 or 2048 bits in length.
The difference between hashing and encryption
| Hashing | Encryption | |
| The process | The process involves transforming the information into a shorter fixed value. It is the key that corresponds to the original message. | The process involves encoding the data such that only the authorized entity can decipher the message. It involves the use of Public Key Infrastructure (PKI). |
| The characters | After hashing, the characters are unreadable and are of a fixed length. | After encryption, the characters are unreadable and are not of a fixed length. |
| Security | More secure | secured but a private key should remain confidential. |
| Information length | The hashed information is of fixed length and is generally small. It will not grow even though the length of the information increases. | The length of encrypted information is never fixed. If the length of the information grows, the length of the encrypted one will increase too. |
| Reverse process | The hash code cannot be reversed at all. | The original message can be retrieved using a designated key. |
Conclusion
There has been a severe increase in the number of successful data breaches across businesses of all sizes. As a result, it becomes necessary to adopt adequate security procedures to prevent these attacks. You can prevent these attacks by encrypting the messages that you wish to transfer. It encodes the message to ensure the confidentiality of the underlying information. As a result, only the designated recipient can decipher the information.
Difference Between Hashing and Encryption
Before understanding the difference between Hashing and Encryption, let us discuss encryption and hashing briefly.
Encryption:
Encryption is a process of converting plaintext into an encoded message that is in an unreadable format. An encrypted message can be decrypted with a key. Modern encryption works on a public key and private key for encryption and decryption purposes.
Hashing:
Hashing converts plaintext into a hash key with the use of a hash function. The hash keys reside in a database and compare whether the original information is matched or not. Hashing is used to store login passwords.
| Encryption | Hashing |
|---|---|
| Encryption is used to encrypt the information while on other hand, the intended receiver can only decrypt the information. | Hashing is used to create a key that signifies the original information. |
| Encryption transforms the data into an encoded format and keeps it a secret from prying eyes. | Hashing retrieves data from the database and indexes it. |
| The original information can be fetched again. | The original information cannot be recovered. |
| Encryption is less secured than Hashing. | Hashing is more secure than encryption. |
| Encryption always creates a new key for each data. | Hashing sometimes creates the same key for new information. |
| RSA, AES, Blowfish are examples of encryption | MD5, SHA-256 are few examples of hashing function. |
| The size of encrypted information will be increased with the growth in the information. | The size of hashed information remains the same even the length of the information is increased. |
| Encryption is a two-way function (encryption and decryption) | Hashing is a single way function that changes information into an irretrievable digest. |
Furthermore, the other procedure you can utilize is hashing. Mapping of the data size of any length to a fixed length. It is a one-way function, and it is technically infeasible to reverse the hashed message. Nevertheless, they are both ideal in handling data security. finally, future enhancements are underway to provide more teeth against possible cyberattacks.